Trezor Login: A Complete Beginner-to-Advanced Guide
Learn how to securely log in to Trezor, protect your assets, and avoid common mistakes while managing your cryptocurrency safely.
Why Does “Trezor Login” Matter?
Unlike logging into a traditional bank account or an online app with just a password, Trezor login is built around hardware-level security. This means you aren’t typing your private key or seed phrase into a website — instead, you’re confirming access through your Trezor hardware wallet, which keeps your keys offline.
For beginners, think of it like this: instead of writing your ATM PIN on a sticky note and leaving it in the open, you keep your PIN locked inside a secure vault. Every time you log in, you use the vault itself to approve access. That’s the essence of Trezor login.
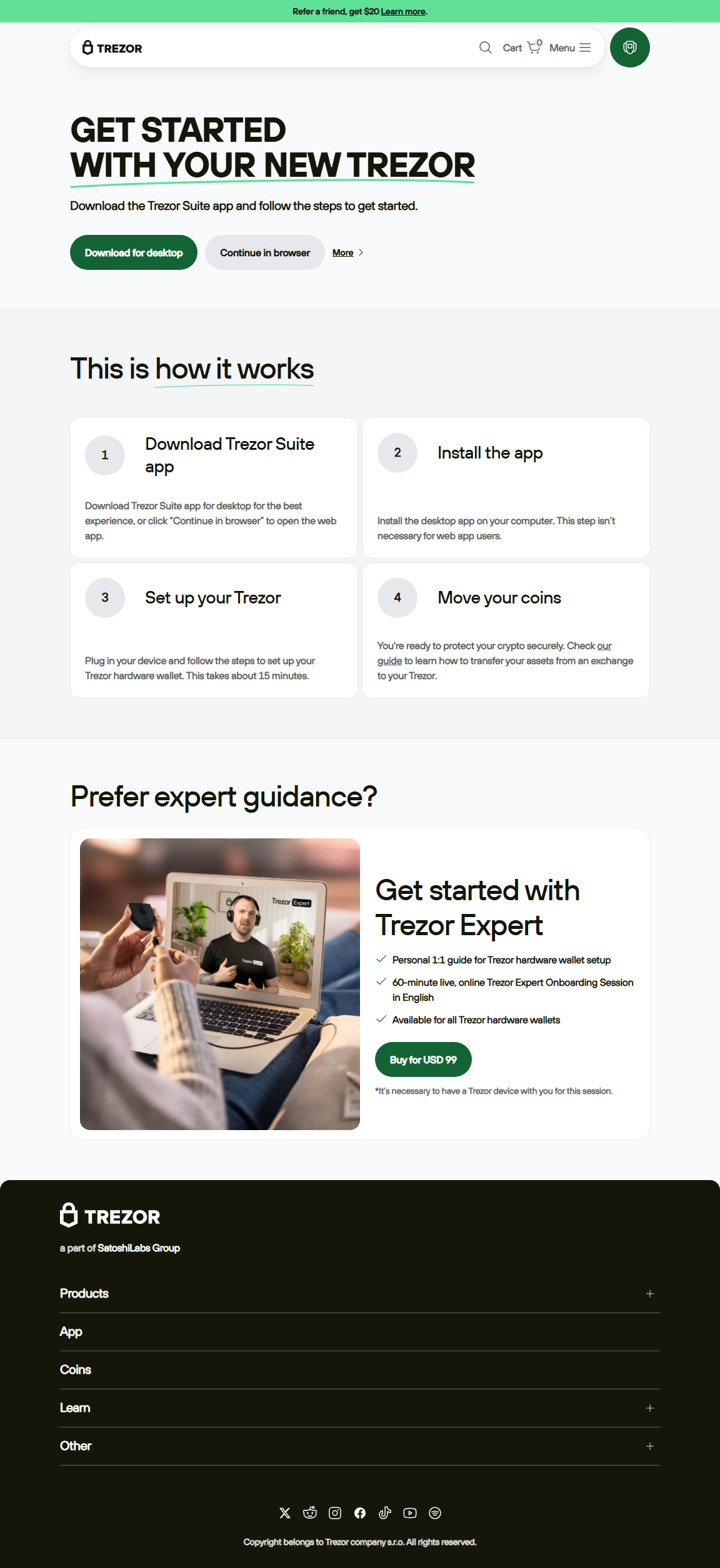
Step-by-Step: How to Log In with Trezor
- Connect Your Trezor Device: Plug your Trezor One or Model T into your computer using the USB cable.
- Open Trezor Suite: Download and launch the official Trezor Suite app (desktop or web version).
- Device Detection: The app will automatically detect your device. If it’s your first time, it may ask you to install firmware or set up your wallet.
- PIN Entry: On-screen you’ll see a scrambled PIN matrix. Enter the correct PIN using your computer while cross-checking on the device display.
- Optional Passphrase: Advanced users can enable a passphrase, which acts like a “second password” for hidden wallets.
- Access Granted: Once verified, you’re inside Trezor Suite where you can manage accounts, send/receive crypto, and track your portfolio.
Trezor Login vs Traditional Logins
| Feature | Trezor Login | Traditional Login |
|---|---|---|
| Security | Private keys offline, PIN + passphrase required | Relies on server-side storage, vulnerable to hacks |
| User Experience | Extra step with hardware confirmation | Quick, but less secure |
| Resistance to Phishing | Device verifies addresses independently | High risk of password phishing |
Best Practices for a Safe Trezor Login
- Always use the official Trezor Suite app, never third-party clones.
- Verify that your device firmware is up to date before logging in.
- Do not enter your recovery seed into any computer or website. It only belongs offline.
- Enable the passphrase option for an extra security layer if you hold large funds.
- Avoid using public or compromised computers for Trezor login.
An Analogy: Trezor Login as a Digital Vault Key
Imagine owning a vault with priceless items inside. To open it, you don’t just type a password into a website — you physically hold the vault key, and you must insert it to unlock access. Trezor login works the same way: the “key” is your hardware device, and without it, nobody can get into your vault, even if they know your PIN layout. This physical link between you and your crypto is what makes Trezor login uniquely secure.
Advanced Tips for Trezor Login
- Use Hidden Wallets: With passphrase-protected accounts, you can create “decoy wallets” for extra privacy.
- Multiple Accounts: Manage separate accounts for business, long-term holding, and daily spending under one login session.
- Tor Integration: Combine Trezor Suite with Tor for maximum privacy during login and transactions.
- U2F Authentication: Use your Trezor as a physical 2FA device for web logins outside crypto.
Frequently Asked Questions about Trezor Login
1. Can I log in to Trezor without the device?
No. The login requires the hardware device because it’s the only place where your private keys are stored. Without it, access is impossible by design.
2. What if I forget my PIN?
You can reset your device using your recovery seed. This will wipe the device and restore all accounts, but you must have the recovery phrase securely backed up.
3. Is Trezor login beginner-friendly?
Yes! While it may seem technical at first, the guided steps on Trezor Suite make it straightforward. The visual PIN layout is designed for extra protection but is easy to learn quickly.
4. Can I use Trezor login on mobile?
Currently, Trezor Suite works best on desktop, but mobile support is expanding. For now, login and transactions are most secure when performed on a computer.
Conclusion: Why Trezor Login Sets the Standard
Trezor login is more than just a way to enter your crypto wallet — it’s a security model built for the future. By requiring a physical device, a PIN, and optional passphrase, it ensures that hackers cannot access your funds even if your computer is compromised. For beginners, this means peace of mind. For mid-level users, it offers advanced tools like hidden wallets and Tor integration. In the world of digital finance, where one mistake can cost a fortune, Trezor login is your strongest ally.